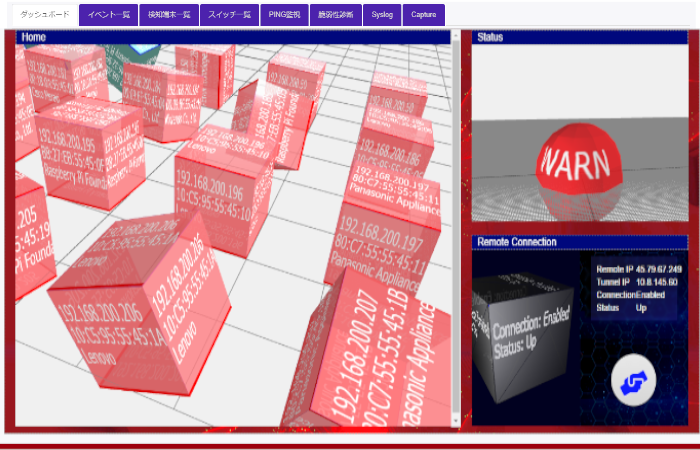
SecurusRadius
Authentication RADIUS server compatible with Captive Potal. In cooperation with the authentication switch and UTM, the new terminal automatically ridirects to the user registration page.
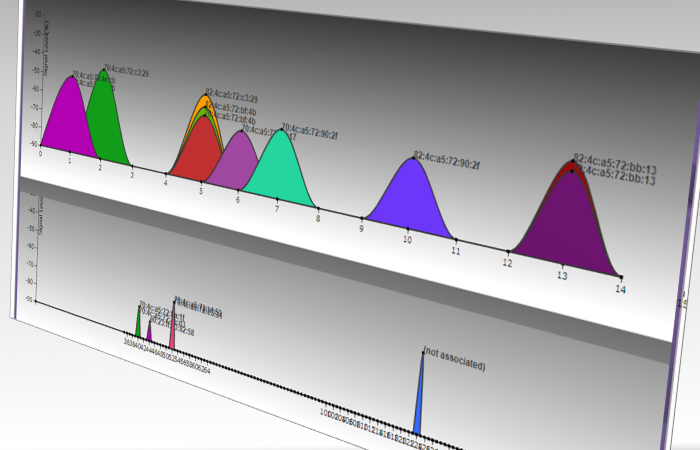
SecurusWifi
Visualize the radio wave condition of WIFI radio. Understanding the radio wave condition is important for installing wireless LAN access points and troubleshooting connections.