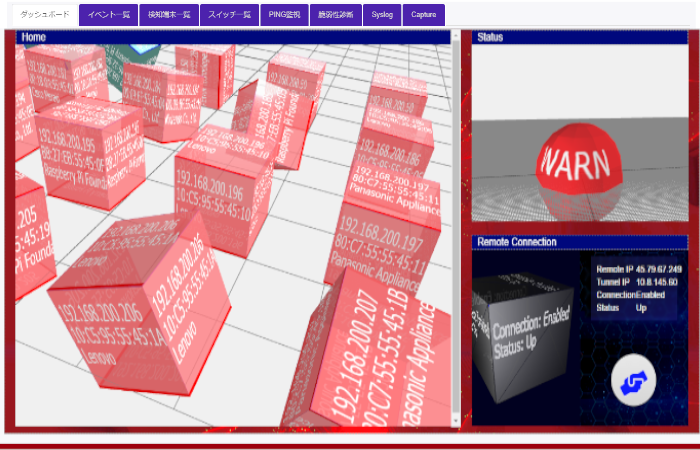
SecureRadiusCap
Authentication RADIUS server compatible with Captive Potal. In cooperation with the authentication switch and UTM, the new terminal automatically ridirects to the user registration page.
How to structure your CSIRT or SOC team
Every organizations be prepared to respond to disruptive cyber incidents. Get in touch with us today for a no obligation cyber security assessment. We can help kickstart your journey to becoming secure.

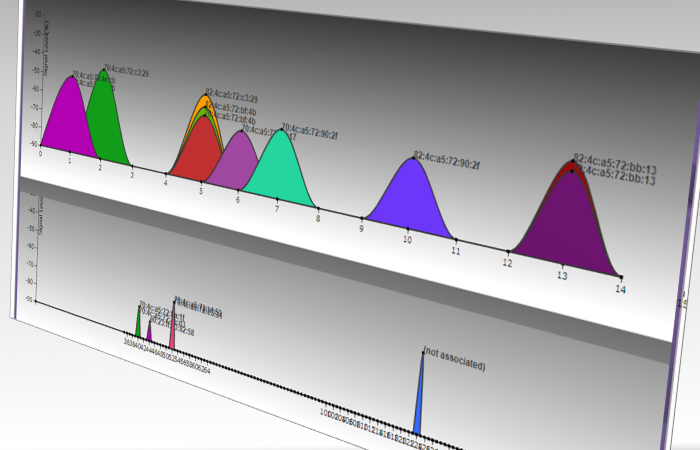
SecurusWifi
Visualize the radio wave condition of WIFI radio. It is important to know the radio wave condition for the installation of wireless LAN access points and troubleshooting.